Invisible Shields: The Intricacies of Protected text
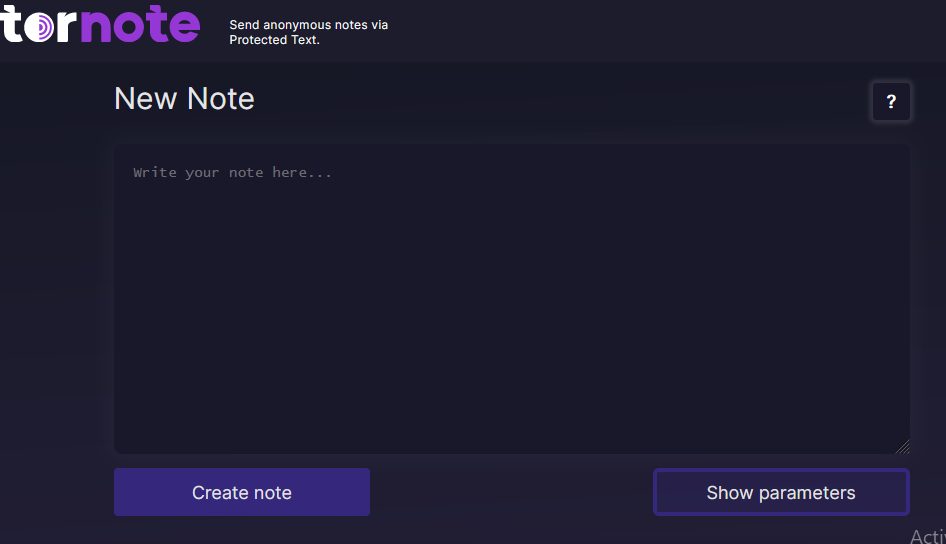
In the age of electronic digital multimedia, information and facts can easily be duplicated, adjusted, and shared with a person with simply a click of a button. This may cause safeguarding delicate details more essential than before. Shielding words can be a vital instrument to guard information and ensure that this remains to be concealed from prying view. In this particular post, we shall check out the skill of protected text understanding shielding terms and how they may be employed efficiently.
Shielding terms are a number of letters, numbers, and heroes employed to imprecise vulnerable details. Just about the most frequent instances of shielding words and phrases is passwords. A great pass word should consist of a mix of lowercase and uppercase letters, amounts, and particular figures such as @, Andamp, and Per cent. This may cause the security password tougher to guess or crack, but in addition more difficult to keep in mind. To make it less difficult, use an acronym or even a recollection technique to help you keep in mind the security password.
Another kind of shielding terms is file encryption. File encryption is the method of changing basic text message into an encrypted message to avoid not authorized gain access to. The encryption important is needed to gain access to the original message, which makes it virtually out of the question for anyone without having the answer to see the initial message. Encryption is typically used to safeguard sensitive on-line dealings like business banking and store shopping.
Shielding terms may also be used to safeguard personal documents. Redacting vulnerable details with black night clubs or asterisks is a common means of shielding terms on papers. This makes the text unreadable by anybody who must not have accessibility to the info. Nevertheless, it’s important to remember that redaction doesn’t always completely take away the information from the document. In some cases, the written text can still be retrieved utilizing specialised software.
Another way to use shielding words is simply by disguising delicate information and facts with code words or slang. This can be frequently used in configurations where delicate details are transported over an open connection route. Using rule words prevents other folks from learning the true concept of your message, keeping it secret from undesirable fans. Even so, it’s crucial to make certain that all events active in the communication are aware of the code words and phrases getting used.
In a nutshell:
Shielding words and phrases certainly are a important device in protecting sensitive info. From passwords and encryption to redaction and computer code phrases, there are many techniques which you can use dependant upon the condition. It’s crucial that you understand the different types of shielding terms and how they can be utilized properly to guard important info. In today’s computerized entire world, learning the art of protected text is essential to maintain level of privacy and protection.